AWS Security Blog
Tag: AWS CloudHSM
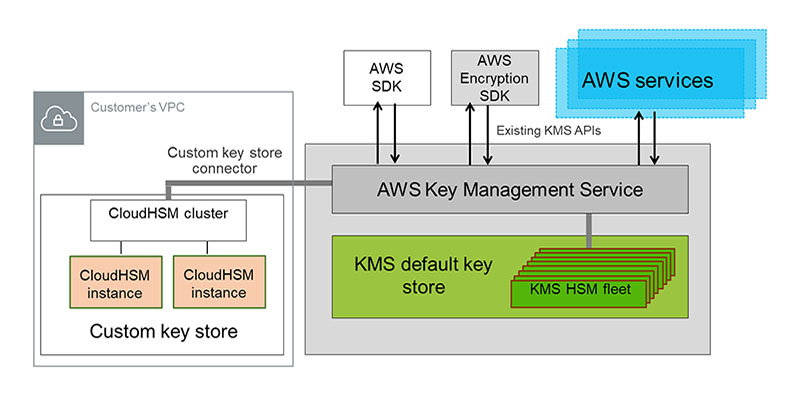
Are KMS custom key stores right for you?
October 29, 2021: AWS KMS is replacing the term customer master key (CMK) with AWS KMS key and KMS key. The concept has not changed. To prevent breaking changes, AWS KMS is keeping some variations of this term. More info. You can use the AWS Key Management Service (KMS) custom key store feature to gain […]
How to clone an AWS CloudHSM cluster across regions
Feb 17, 2025: This blog post references AWS CloudHSM Client SDK 3, which is no longer the recommended version. AWS recommends that you use the latest version, AWS CloudHSM Client SDK 5, which provides updated functionality and commands. We are currently working on an updated blog post for CloudHSM Client SDK 5. See the AWS […]
Using AWS CloudHSM-backed certificates with Microsoft Internet Information Server
Feb 17, 2025: This blog post references AWS CloudHSM Client SDK 3, which is no longer the recommended version. AWS recommends that you use the latest version, AWS CloudHSM Client SDK 5, which provides updated functionality and commands. We are currently working on an updated blog post for CloudHSM Client SDK 5. See the AWS […]
How to Update AWS CloudHSM Devices and Client Instances to the Software and Firmware Versions Supported by AWS
Note from September 18, 2017: In this blog post, “AWS CloudHSM” refers to the product that’s now known as AWS CloudHSM Classic. As I explained in my previous Security Blog post, a hardware security module (HSM) is a hardware device designed with the security of your data and cryptographic key material in mind. It is […]
In Case You Missed These: AWS Security Blog Posts from June, July, and August
In case you missed any AWS Security Blog posts from June, July, and August, they are summarized and linked to below. The posts are shown in reverse chronological order (most recent first), and the subject matter ranges from a tagging limit increase to recording SSH sessions established through a bastion host. August August 16: Updated […]
How to Remove Single Points of Failure by Using a High-Availability Partition Group in Your AWS CloudHSM Environment
A hardware security module (HSM) is a hardware device designed with the security of your data and cryptographic key material in mind. It is tamper-resistant hardware that prevents unauthorized users from attempting to pry open the device, plug any extra devices in to access data or keys such as subtokens, or damage the outside housing. […]